Introduction Infrastructure management must be done effectively and consistently in today’s fast-paced software development environment. Infrastructure as Code (IAC) has become a potent strategy for managing and automating infrastructure deployments. This article will discuss IAC and Pulumi, a cutting-edge IAC technology that enables programmers to create and manage infrastructure using well-known programming languages. Infrastructure as […]
In a quest for greater flexibility and efficiency, Samsung Electronics discovered a seamless partner in Amazon Web Services (AWS). Within a mere span of 18 months, Samsung Electronics orchestrated a momentous migration, transferring its extensive global Samsung Account data to the ethereal embrace of Amazon Aurora. This cloud-native, MySQL- and PostgreSQL-compatible relational database proved to […]
Introduction Welcome to this comprehensive guide on MLOps on AWS. In this article, we will explore the world of MLOps (Machine Learning Operations) on the AWS (Amazon Web Services) platform. MLOps brings together the disciplines of machine learning and DevOps, enabling organizations to effectively develop, deploy, and manage machine learning models at scale. By leveraging […]
Introduction In the digital age, ensuring fast and reliable content delivery is crucial for providing an exceptional user experience. Content Delivery Networks (CDNs) play a significant role in achieving low-latency and high-availability content delivery. AWS Global Accelerator is a powerful service from Amazon Web Services that simplifies the process of setting up a global CDN. […]
Let’s explore the ins and outs of IT support services including Cloud Migration, DevOps and Cybersecurity – There is a wealth of resources available to businesses and individuals alike. So grab a cup of your favorite coffee, and let’s dive headfirst into the world of IT support in Dubai! The Importance of IT Support in […]
Cloud computing has transformed the IT industry drastically by providing on-demand access to computing resources such as servers, storage, databases, and software applications over the internet. This has drastically reduced the time and cost involved in setting up and maintaining an IT infrastructure. Previously, organizations had to invest a significant amount of money and time […]
In this article we are going to discuss the services and components invloved in AWS Security Automation. These components are designed to work together to provide a comprehensive and automated approach to securing AWS resources and applications. By using these tools organizations one can not only reduce the risk of security breaches but also streamline […]
Docker has revolutionized the IT industry by stepping in 2013 as a platform that uses OS-level virtualization to expose software applications to the internet. By leveraging the containerization model, the earlier problems faced by development and operations teams have been mitigated. In the digital transformation era, we could see some formerly advanced methods and technologies […]
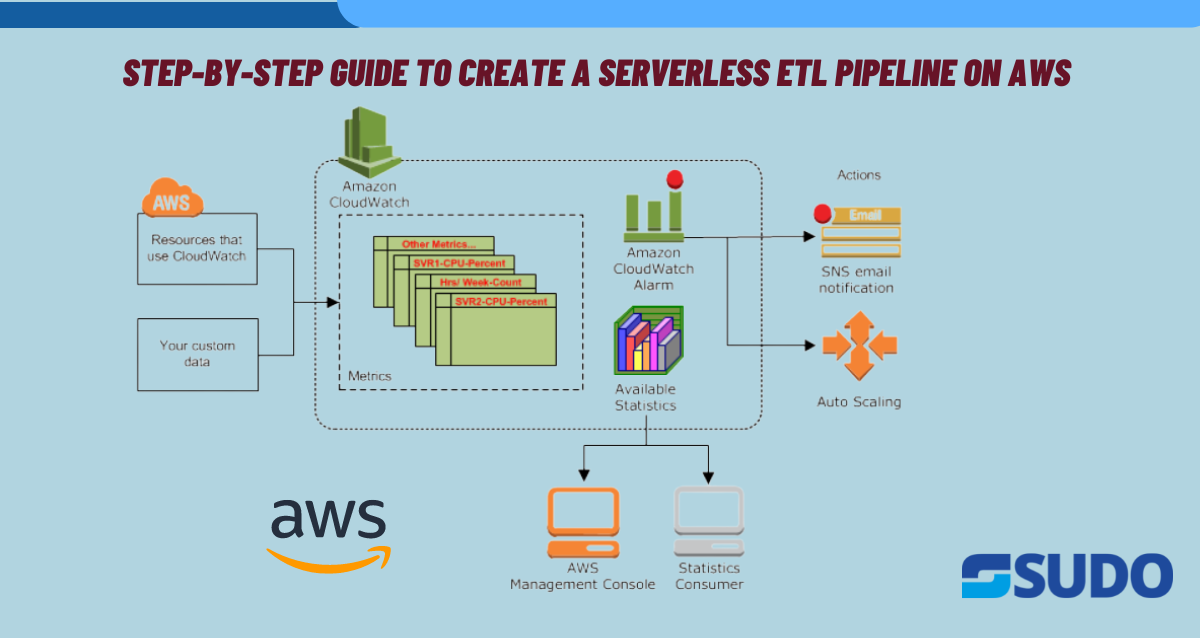
Why ETL Pipelines? Serverless ETL pipelines are becoming increasingly popular because they offer a number of benefits over traditional ETL pipelines. Here are some reasons why and for which projects ETL serverless pipelines are created: Use Cases ETL serverless pipelines can be used for a wide range of projects, including: Steps Creating a Serverless ETL […]
Why is AWS security important? AWS security is important for protecting an organization’s sensitive data, ensuring business continuity, complying with regulations, and mitigating security risks. It helps prevent financial losses, reputational damage, legal liabilities, and loss of customer trust. AWS security measures such as encryption, access controls, and monitoring can help prevent data breaches and […]